The IT-AI Protection Manual
A Modern IT Leader’s Guide To Combat Evolving Threats
The Dark Side of AI: Why Your Security Manual Needs an Upgrade
Modern IT management asks a lot of you. When you’re the one on the front lines daily, it’s a constant battle to keep everything under control and secure. You’re pulled in ten different directions, for ten very good reasons… and they all need you now. But you’re used to managing a rapidly-growing, ever-changing environment with limited resources, so you handle it like the pro you are.
But now, a new, powerful force is making your world more diverse (and more dangerous) than ever before: Artificial Intelligence (AI).
This is not a guide about generative AI, agentic AI, or any AI initiative you have been asked to lead on behalf of your organization.
This is about the fact that AI-driven threats are now the #1 security concern for a majority of IT leaders (56%).
Whether you have a dedicated security team or not, and the threats are getting smarter, faster, and harder to spot. They’re targeting your people and your technology with a level of precision that didn’t exist just a few years ago.
The central idea is simple: AI isn’t just creating entirely new attacks… it’s supercharging existing ones.
Phishing emails are no longer riddled with typos; they’re grammatically flawless and personalized. Malware adapts and changes to evade your defenses. The attacks you’ve always dealt with are now faster, more sophisticated, and more dangerous.
The best defense is a layered approach that combines a well-informed staff with a well-maintained suite of technology.
This manual is your guide to building a more resilient security posture. We’ll provide you with a clear, actionable strategy to combat these evolving threats.
Each part of this series will focus on a specific, AI-enhanced threat. We will explore what the attack is, how AI is boosting it, and how to train your team and secure your technology to fight back.
By the end, you’ll have a playbook for building an AI-ready security strategy—before it’s too late.
01 AI-Powered Phishing and Social Engineering
Is Your Inbox a Trap?
1.1 What is Phishing?
At its core, phishing is a type of social engineering, which is an attack that preys on human psychology. Instead of exploiting a technical vulnerability in a system, it manipulates a person into giving up sensitive information, downloading malware, or sending money.
While social engineering can take many forms, phishing, smishing, and vishing are the most common. The primary goals of these attacks are to steal credentials, deliver malware, or commit financial fraud.
1.2 How Does AI Boost This Attack?
In the past, many phishing attacks were easy to spot due to poor grammar, generic greetings, and other simpler tells. Now, generative AI has changed the game. AI can create highly convincing, personalized, and grammatically flawless emails and texts. It can also analyze public data to craft messages that perfectly mimic trusted contacts or companies, making them incredibly difficult to distinguish from legitimate communications.
Plus, AI can manipulate voice and language, enabling attackers who speak a foreign language to sound like native speakers.
1.3 Are You a Target? A Quick Susceptibility Quiz
To understand your company’s susceptibility to these threats, ask yourself and your team these questions:
-
Do all critical accounts (email, financial, and cloud services) in your company have Multi-Factor Authentication (MFA) enabled?
-
Do your employees regularly receive security awareness training specifically on phishing?
-
Does your organization have a clear, easy-to-use process for employees to report suspicious emails or messages?
-
Are there policies in place for verifying requests for sensitive information or financial transactions?
-
Are your email security filters up-to-date and configured to detect advanced threats?
The more “no” answers you have, the higher your risk of falling victim to an AI-powered phishing attack.
1.4 How To Train Your Team For This Threat
Your employees are your first line of defense, so you need to empower them with the knowledge and skills to spot a scam.
Phishing Simulation Campaigns
Use a phishing simulation platform to test your team’s vigilance. Start with simple lures and then move to more advanced, AI-enhanced impersonations of the CEO or other leadership roles. This measures employee susceptibility and identifies who needs more training.
Vishing/Smishing Drills
These drills help test employee vigilance against voice or text-based scams. The goal is to instill a “trust but verify” mindset, where employees are trained to question unusual requests, even if they seem to come from a familiar source.
1.5 How To Secure Your Tech Stack For This Threat
Human training is crucial, but technology provides a vital safety net. Here’s how you can secure your systems to combat AI-powered phishing:
Modern solutions use AI and machine learning to detect malicious behavior rather than just relying on known signatures. They can spot unusual language, urgency, or requests that don’t fit normal patterns.
This is the single most effective technical control against credential theft. Even if an AI-crafted email tricks an employee into entering their password, MFA provides a critical second layer of defense that makes it harder for an attacker to gain access.
This solution blocks access to known malicious websites at the network level. If an employee clicks on a malicious link in an email, DNS filtering can prevent them from even reaching the fraudulent site.
02 Deepfake-Enabled Fraud and Impersonation
Don’t Trust Everything You Hear (Or See)
2.1 What is Deepfake-Enabled Fraud?
Deepfake-enabled fraud is a form of social engineering that takes advantage of our assumption that what we see and hear is real. This type of fraud can exist even without AI. However, AI has supercharged this attack by allowing criminals to create highly realistic fake audio and video, known as deepfakes, to impersonate individuals.
The most common targets are those in positions of authority, like CEOs. For example, an attacker could use a cloned voice of a CEO to instruct an employee to make a fraudulent wire transfer.
2.2 How Does AI Boost This Attack?
AI can now realistically clone a person’s voice or likeness from publicly available data, making the technology highly accessible to bad actors. The quality of deepfakes has become so good that traditional visual or auditory cues, like a strange voice inflection or a glitch in a video, are no longer reliable indicators of fraud.
Common vectors include:
2.3 Are You a Target? A Quick Susceptibility Quiz
To assess your risk, take this short susceptibility test by answering the following questions:
-
Does your company have a strict, multi-step verification process for all financial transactions, particularly wire transfers?
-
Are your employees aware that voice and video calls can be faked?
-
Do you have a unique verification method for high-stakes requests (a pre-arranged code word or a policy to call back on a pre-established, known number)?
-
Is your leadership team aware of the risks of publicly available audio and video content that could be used to train deepfakes?
The more “no” answers you have, the higher your risk of falling victim to a deepfake-enabled fraud attack.
2.4 How To Train Your Team For This Threat
Since deepfakes are designed to bypass human trust, your training must focus on procedural and behavioral responses.
Implement a mandatory “out-of-band” verification process for all high-value transactions or sensitive data requests. This means if a request comes via email or even a voice call, the employee must verify it by calling back on a known, pre-established phone number—not the one provided in the suspicious communication.
Run a role-playing scenario to test your team’s response to a deepfake attack. A good scenario would be a deepfake video call from your CEO requesting an urgent wire transfer. This exercise helps identify procedural and human response gaps before a real attack occurs.
Encourage a culture where employees feel comfortable questioning any urgent or unusual requests, regardless of who they appear to be from. This is especially important for new employees, who may not have a history interacting with executives.
2.5 How To Secure Your Tech Stack For This Threat
Your technology can limit the damage of a successful impersonation attack.
Unified Communications (UC) Platform Security
Platforms like Zoom or Microsoft Teams have security features that can prevent deepfake attacks. Ensure your settings require participants to be verified and use features like meeting waiting rooms to prevent an attacker from seamlessly joining a call.
Identity and Access Management (IAM)
The principle of least privilege, a core part of IAM, ensures employees only have access to the data and systems they need for their jobs. By restricting access to sensitive systems, you limit the damage an employee can inadvertently cause if they fall for a deepfake.
03 AI-Enhanced Malware and Ransomware
Hope For The Best, Prepare For The Worst
3.1 What is Malware and Ransomware?
Malware, or malicious software, is a broad term that describes any software designed to disrupt computer operation, gather sensitive information, or gain unauthorized access to computer systems.
Ransomware is a type of malware that encrypts a victim’s files and demands a ransom payment to restore access. Attackers often follow a typical attack chain, gaining initial access through a vulnerability, moving laterally through the network, and then deploying the ransomware.
3.2 How Does AI Boost This Attack?
AI makes malware more intelligent and adaptable by making it “polymorphic,” meaning it can change its own code to evade traditional, signature-based antivirus solutions. Also, AI-augmented tools can automate the process of vulnerability scanning and exploit development, accelerating the entire attack process from months to mere hours.
Polymorphic Malware
An attacker targets a device through a typical attack vector which installs a strain of polymorphic malware.
Malware connects back to AI hub, is fed payload to exploit system at runtime.
Changes function names, variables, code structure, keys, and more to avoid detection.
Stolen data is sent to central control plane as malware evades signature-based antivirus.
3.3 Are You a Target? A Quick Susceptibility Quiz
To gauge your company’s readiness, consider these questions:
-
1
Do you have a robust, isolated, and regularly tested backup strategy for all your critical business data?
-
2
Do you have an automated patch management system to ensure all operating systems and applications are updated?
-
3
Do you have an established and defined incident response plan for a ransomware attack?
-
4
Do you have an Endpoint Detection and Response (EDR) solution that goes beyond basic antivirus?
-
5
Is your network segmented to contain an infection and prevent it from spreading?
The more “no” answers you have, the higher your risk of falling victim to a malware/ransomware attack.
3.4 How To Train Your Team For This Threat
While a ransomware attack is primarily a technical problem, training your team is still a vital defense.
Ransomware Incident Response Tabletop Exercise
Gather key personnel from IT, management, finance, and legal to walk through a simulated ransomware attack. The goal is to identify and fix gaps in your response plan, clarify roles and responsibilities, and ensure everyone knows what to do in a crisis.
Training on Safe Practices
Remind employees about the importance of not opening suspicious email attachments or clicking on unknown links, as these are still common delivery methods for malware.
3.5 How To Secure Your Tech Stack For This Threat
Endpoint Detection and Response (EDR) / Next-Generation Antivirus (NGAV)
Upgrade from traditional antivirus to an EDR or NGAV solution. These solutions use behavioral analysis to detect and block malicious activity, making them far more effective against adaptive, AI-enhanced malware.
Patch Management Systems
Automated patch management is crucial to close known vulnerabilities that AI-powered tools can quickly find and exploit. When this process is centrally managed, you have a lot of control to push critical updates and communicate urgency to end users.
Robust Backup and Disaster Recovery (BDR)
This is the ultimate defense against ransomware. Implement the “3-2-1-1” backup rule: keep three copies of your data, on two different media, with one copy offsite and at least one copy that is immutable (meaning it cannot be altered or deleted).
Network Segmentation
By dividing your network into isolated segments, you can limit the lateral movement of malware and contain a breach, preventing widespread damage. Applying the principles of least privilege to network segments will minimize exposure and give you more control.
Your Roadmap for AI-Ready Security
This manual has provided a roadmap for understanding, assessing, and strengthening your defenses against the top three AI-enhanced threats. We’ve focused on leveraging existing, proven technologies and refining your use of them to combat this new wave of attacks.
At the heart of all of these attacks—whether it’s a deepfake voice scam or an AI-enhanced phishing email—is the goal of compromising an identity. In cybersecurity, your identity is the “keys to the kingdom” for attackers. The most critical step you can take is to protect that identity and the devices it accesses.
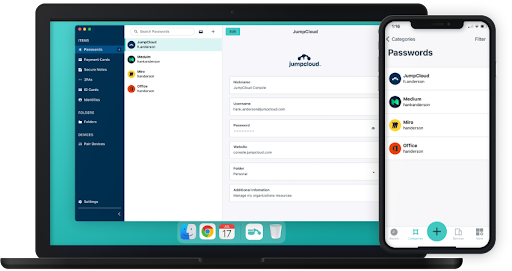
This is where JumpCloud can help. By using the JumpCloud platform, you can implement the necessary technology solutions—such as MFA, least privilege, and conditional access policies—to protect your identities and devices and build a more resilient security posture.
Want to learn more? Check out how JumpCloud can help you implement the security best practices outlined in this manual.
Want to Learn More?
Check out how JumpCloud can help you implement the security best practices
Try for Free